Hazy (Hash,Zappy) // hash and symmetric-encryption tool
Benefits of Hazy
Trust that your data is safe
Key guess attempts are very slow for large keys
because the key accepts any non-zero numeric value.
Gain Time
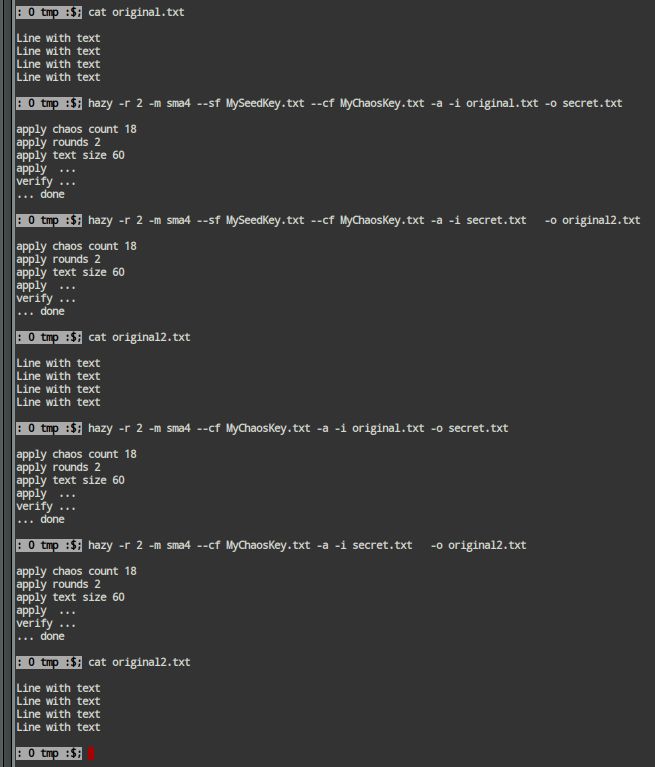
This tool is, by design, fast at encryption/decryption
even with long keys.
Uniqueness of Hazy
- Key length and number of rounds are limited only by computer capabilities.
When to use Hazy?
- You can use encryption to keep your backups secure.
- When secure data exchange and speed and responsiveness are important, this is the right tool to use.
Who can use Hazy?
- Anyone who wants to encrypt a file can use this tool.
Hazy Feature List
- Hash tool for text or binary data.
- Multiple hashing algorithms can be used.
- Symmetric Encryption tool:
- Variable key length: 32bit to 1024bit and beyond.
- The upper limits are dictated by: the used computer, OS and what is reasonable from the user point of view.
- The given key is a base for the real, variable key.
- It was designed to be fast at encryption/decryption.
- However, bigger keys can slow down a bit the encryption/decryption process.
- It was found to be faster than AES for the same key length and the same number of rounds.
- It was designed to be slow at guessing keys.
- Any non-zero number can be used as key chunks. It is not limited to prime numbers. Multiples of 2 are not recommended.
- The big range of possibilities for key and seed makes it harder to guess the key.
- Allow multiple rounds, which are recommended for short text.
- Easy to use.
- A long key can be generated from text, with the same tool.
Notes:
- Please use long keys (and keep them in a safe place) and long text/binary data (pad with random data if necessary).
- There is no known method of guessing long keys in a reasonable amount of time.
- There are no known practical shortcuts to guessing a long key.
- The actual value for "short" and "long" depends on the security level desired by the user for a particular task.
- Some practical examples can be found in Downloads.
See also:
Download and Try , then Buy
 Hazy video demo with symmetric encryption
Hazy video demo with symmetric encryption